Kali Linux for Pentesting
31 May 2013 Braintree hosted a Hax ‘n Snax event this afternoon. Devs from around Chicago gathered together to hack on code, socialize, trade ideas, and hone skills. Thanks Braintree for putting on a great event.
Braintree hosted a Hax ‘n Snax event this afternoon. Devs from around Chicago gathered together to hack on code, socialize, trade ideas, and hone skills. Thanks Braintree for putting on a great event.
My Hax ‘n Snax time was spent interacting with other devs and experimenting with a Linux distro that I just discovered, Kali Linux.
What is Kali Linux?
Kali is a fairly new Linux distro designed for digital forensics and penetration testing. If you’re looking for a general purpose Linux distro, Ubuntu would be a better choice. Kali is the successor of BackTrack. The developers of Kali and BackTrack, Offensive Software, state that “Kali is a more mature, secure, and enterprise-ready version of BackTrack Linux.” You can download it at Kali.org.
Parallels Installation Gotcha
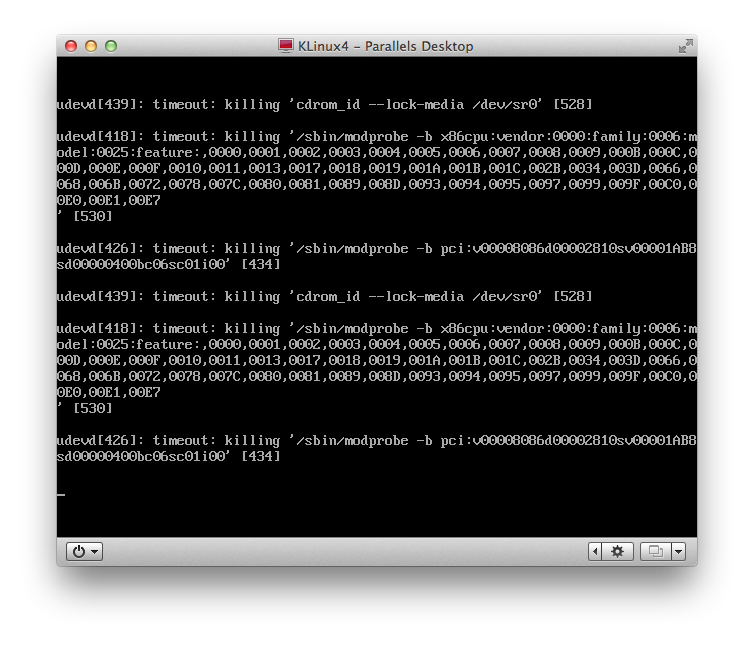
I’m running Kali Linux inside of Parallels version 7 on Mac OS X 10.8.3 (Mountain Lion). The Linux installation proceeded normally, but when I rebooted the virtual machine, Linux wouldn’t come up. Instead, I got the perpetual display of timeouts shown below.
Google led me to a solution on a blog called redrise. The solution: To make Kali run on Parallels, uncheck the check box labeled “Show battery in Linux”, as shown below.
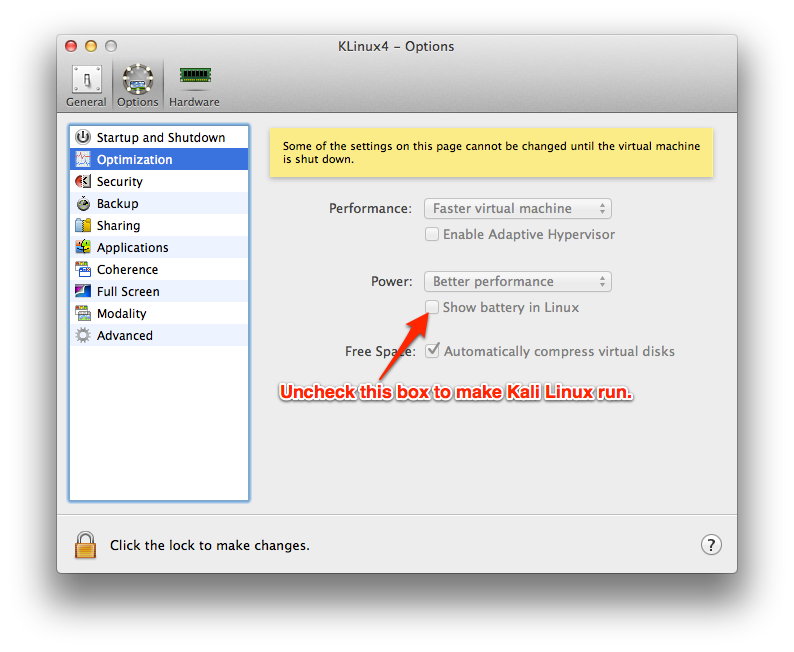
I’m not sure why a battery indicator would prevent Kali from booting in Parallels, but the solution worked. When I installed Kali on VMWare, the OS ran without special configuration changes.
The Kali Linux Tools
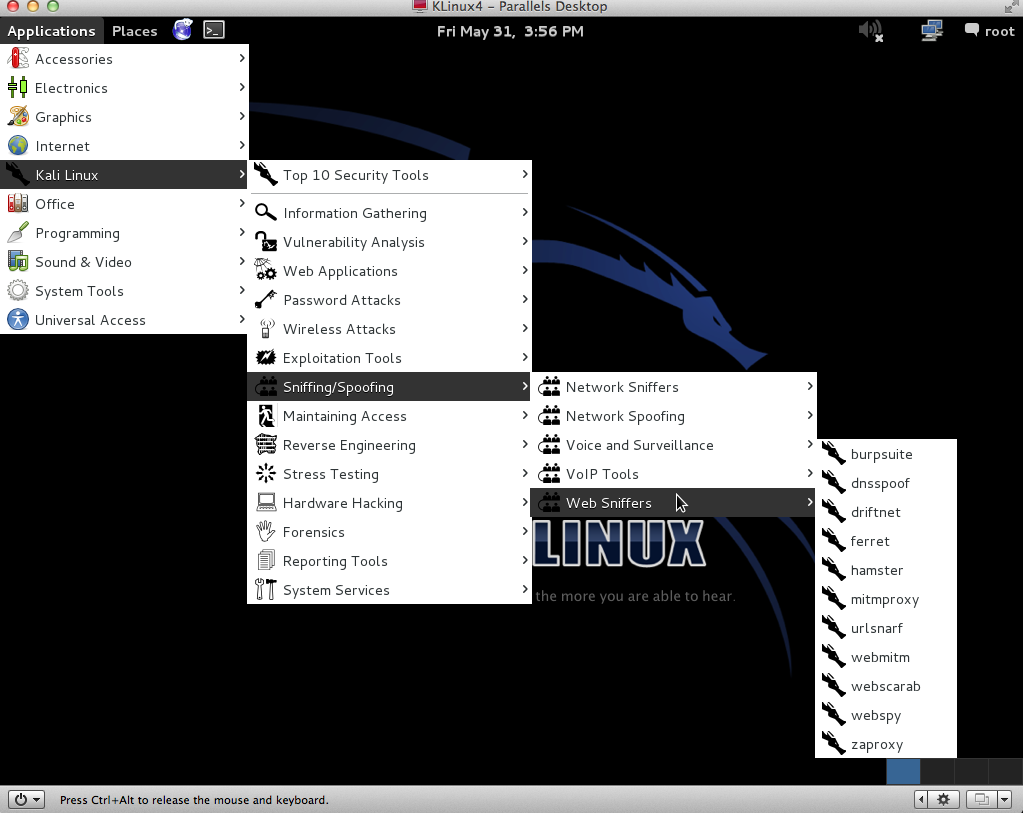
Kali comes with over 300 penetration tools. It’s open source, so if you see room for improvement, fork the repo and go to work. If your ideas are strong enough, the developers might accept your pull request. There’s even a version of Kali for Raspberry Pi. Take a look at the GUI.
Using Wireshark on Kali Linux
Kali includes sniffer tools that can capture WiFi traffic. If the WiFi traffic is “protected” (note the quotes) with an older method like wireless encryption protocol (WEP), Kali’s tools can crack the encryption.
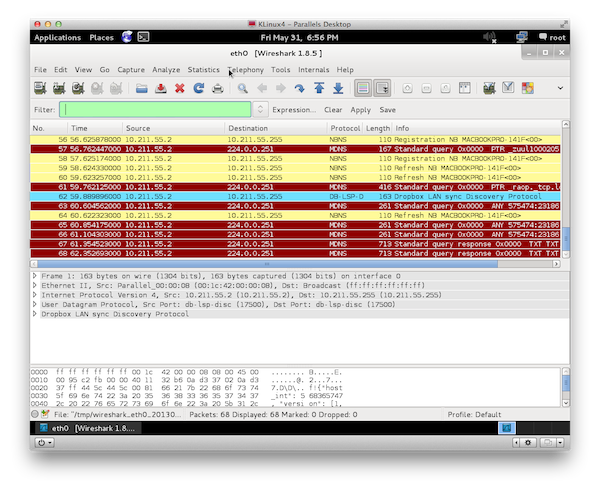
A screenshot from Wireshark appears above. Wireshark sits and observes network traffic. If a packet looks interesting, drill down to discover the packet’s source, destination, and contents.
Summary
Kali enables developers and network professionals to protect themselves and their clients from attacks. Kali is powerful, and with great power comes great responsibility.



